Cyber is Not a Data Problem—It’s a Continuity Crisis

Cyber is Not a Data Problem—It’s a Continuity Crisis
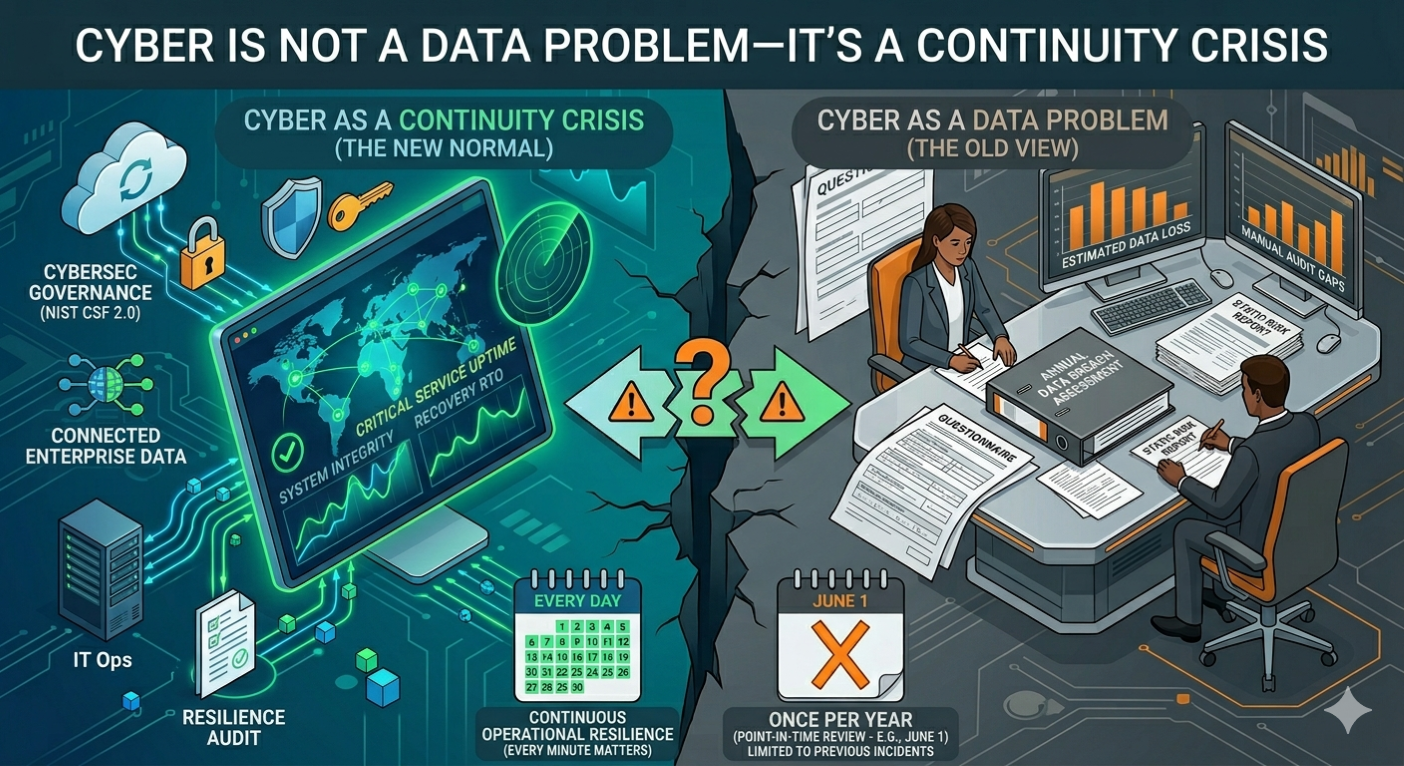
For decades, we in the risk profession have siloed "Cyber" under the IT banner. We treated it as a battle for confidentiality—protecting the "Crown Jewels" from being stolen. But in 2026, the game has changed fundamentally. Cyber is no longer just a security threat; it is the single most significant Business Continuity Management (BCM) event facing the modern enterprise.
When a ransomware group hits a tier-one financial institution today, they aren't just looking for data to sell. They are looking to flip the "off switch" on your critical operations. In this landscape, the distinction between "Cyber Incident" and "Operational Shutdown" has evaporated. If you are still managing cyber as an IT risk, you are effectively flying blind into a continuity crisis.
The Boardroom Pivot: From "Are We Secure?" to "How Long Are We Down?"
The most significant shift we’ve seen in the last 18 months isn't technological; it’s cultural. Boards of Directors have finally stopped viewing cyber through the lens of firewalls and encryption. According to industry analysis from TechRadar, boards now overwhelmingly view cyber as a business continuity risk, not an IT risk.
Source: TechRadar - Cyber resilience is a business imperative (Nov 2025)
This shift is driven by the realization that in a hyper-connected ecosystem, a cyber event is a downtime event. The focus has moved from prevention (which is increasingly seen as impossible to guarantee) to resilience—the ability to weather a disruption and continue core business lines.
Regulatory Gravity: The "Sound Practices" Standard
U.S. regulators have been signaling this shift for years, but the 2026 examination cycle has brought it into sharp focus. The Federal Reserve, OCC, and FDIC have solidified their expectations through the Interagency Paper on Sound Practices to Strengthen Operational Resilience.
Under these standards, the Board is responsible for approving the firm’s "Tolerance for Disruption." This isn't about how much money you can lose; it’s about how many hours or days you can survive without a critical operation before the impact becomes "unsafe or unsound."
"The firm's board of directors approves and periodically reviews its risk appetite for weathering disruption... articulating the firm's tolerance for disruption considering its risk profile and the capabilities of its supporting operational environment."
Source: Federal Reserve - Interagency Paper on Sound Practices to Strengthen Operational Resilience
The Reality of 2026: Ransomware as a Denial-of-Service
What does this look like in practice? The data from Q1 2026 is sobering. The U.S. remains the primary target for global ransomware, accounting for 51% of all verified incidents.
Source: Industrial Cyber - Ransomware reaches elevated 'new normal' in 2026
But the nature of these attacks has evolved. We are seeing:
- Ransomware as a Downtime Event: Threat actors are no longer just exfiltrating data; they are targeting the "control plane" of the organization. If your manufacturing floor or your settlement engine goes dark, the data breach is the least of your worries.
- Identity as the Kill Switch: Identity compromise has become the most effective way to trigger an operational shutdown. By seizing administrative credentials, attackers can lock an institution out of its own recovery environment.
Operationalizing Cyber Resilience: The Path Forward
To bridge the gap between IT and BCM, risk professionals must move toward an integrated model. This requires three tactical shifts:
1. Governance Alignment (NIST CSF 2.0)
The introduction of the "Govern" function in NIST’s Cybersecurity Framework 2.0 has been a game-changer. It forces the integration of cybersecurity into the broader enterprise risk management (ERM) strategy. Cybersecurity is no longer a "sidecar" to the business; it is baked into the roles, responsibilities, and risk-appetite statements of the C-suite.
Source: NIST - Cybersecurity Framework (CSF) 2.0
2. Testing for "Severe but Plausible" Scenarios
Traditional BCM tests for "loss of building" or "loss of power." Cyber BCM must test for "loss of integrity." What do you do when your backups are online but you can't trust the data within them? Resilience means having a "clean room" recovery strategy that can be executed within your Board-approved tolerance for disruption.
3. Third-Party Concentration Risk
As we lean more on cloud providers and SaaS, our "Cyber Continuity" is often in the hands of a third party. Regulators are now scrutinizing Concentration Risk—if five of your critical business lines rely on the same identity provider, and that provider goes down, your BCM plan is effectively moot.
Conclusion
We are in a new era of risk management. The "firewall" of the future isn't just a piece of software; it’s a robust, board-governed operational resilience framework. As risk professionals, our job is to ensure that when the next cyber event hits—and it will—it remains a "security incident" and doesn't become a "continuity catastrophe."
ERM Pilot is built for risk and compliance teams at financial institutions who are ready to stop working for their software and start letting their software work for them. See what's possible →