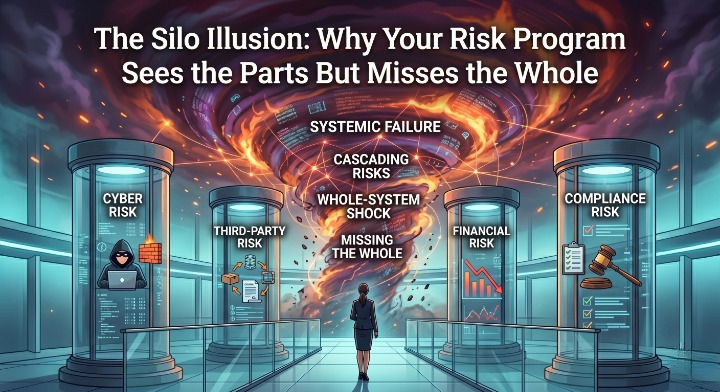
The Silo Illusion: Why Your Risk Program Sees the Parts But Misses the Whole

The Silo Illusion: Why Your Risk Program Sees the Parts But Misses the Whole
Enterprise Risk Management | William C. Hord
Most financial institutions have a credit risk program.
They have an operational risk program.
They have a vendor risk program.
They have a cyber risk program.
What they rarely have is a risk program.
Not in the truest sense of the word. What they have is a collection of well-intentioned, well-documented, professionally managed risk functions — each operating with its own taxonomy, its own reporting cadence, its own definition of what "high risk" means, and its own audience inside the institution.
And that distinction — between managing risk functions and managing risk — is quietly becoming the most consequential gap in financial institution governance today.
The Architecture of the Problem
In two previous pieces in this series, we examined how AI is creating governance blind spots when embedded in risk workflows without proper traceability, and how fragmented data architecture is now a frontline regulatory exposure — not a back-office IT problem.
Both of those issues share a common root cause.
Silos.
Not organizational silos in the traditional sense — the turf wars and communication breakdowns that management consultants have written about for decades. Something more structural than that. More embedded. The silos I am describing are architectural. They are baked into how risk programs were designed, how platforms were purchased, and how reporting was built — long before anyone was asking whether those functions needed to talk to each other in real time.
The result is a risk program that is technically complete and operationally fragmented.
Every domain has its reports. Every report has its audience. And somewhere between the credit risk committee, the operational risk committee, the vendor oversight committee, and the cybersecurity steering committee — the actual picture of enterprise risk gets lost.
What Examiners Are Starting to See
Regulators are not blind to this.
The FDIC's 2025 Risk Review noted explicitly that market and credit risks are increasingly interconnected — and that institutions struggling most in examinations are those whose risk functions cannot demonstrate how exposures in one domain affect exposures in another.
The OCC's Heightened Standards and SR 23-4 guidance from the Federal Reserve both emphasize risk data aggregation that is adaptable, reconcilable, and enterprise-wide. Not department-wide. Not function-wide. Enterprise-wide.
What examiners are beginning to probe — and what will define examination outcomes over the next cycle — is not whether each individual risk program is sound in isolation. It is whether the institution can answer a deceptively simple question:
If a significant vendor fails today, what is the combined credit, operational, cyber, and continuity exposure to this institution — and how quickly can you show me?
Most institutions cannot answer that question in a single conversation. They can schedule four separate meetings.
That is the silo problem made visible.
The Risk Relationship Most Programs Ignore
Here is a scenario that plays out more often than anyone publicly acknowledges.
A mid-size financial institution has a critical technology vendor. That vendor is also a counterparty in a payment processing arrangement. That same vendor's infrastructure hosts core systems that are embedded in the institution's business continuity plan. And that vendor recently experienced a security incident that was disclosed quietly in a contract amendment.
The vendor management team logged the security incident as a vendor risk finding — medium severity, remediation plan requested.
The cybersecurity team was not notified.
The operational risk team was not notified.
The business continuity team did not reassess the RTO assumptions tied to that vendor.
Credit risk never evaluated whether the vendor's financial position had deteriorated.
Every team did their job correctly within their domain. And the institution's aggregate exposure to that single vendor was never actually assessed.
This is not a hypothetical. Variations of this scenario have contributed to real examination findings, real enforcement actions, and real operational failures at institutions of every size.
From Compliance Reporting to Decision Support
The shift that forward-looking institutions are making — and that regulators are increasingly rewarding — is a fundamental reorientation of what ERM is for.
In its traditional form, ERM was designed as a compliance reporting system. Risk registers were maintained to demonstrate to examiners that risks had been identified and documented. Risk ratings were assigned to satisfy governance requirements. Reports were produced on a schedule that aligned with committee meetings, not with the actual rhythm of risk in the institution.
That model was never really about managing risk. It was about evidencing governance.
The institutions pulling ahead of regulatory expectations are treating ERM as a decision support system. Risk information flows to where decisions are being made — in real time, across domains, connected to the actual operational and financial exposures it represents.
The difference is not a software upgrade. It is a fundamental change in what leadership expects the risk function to produce and when.
The Connected Risk Questions No Siloed Program Can Answer
There is a set of questions that matter most to boards, executives, and examiners — and that no siloed risk program is architecturally capable of answering:
Are our credit concentrations also operational concentrations? A large commercial real estate portfolio concentrated in a single geography is a credit risk. It is also an operational risk if your servicing capacity is similarly concentrated. It is a vendor risk if the technology supporting that portfolio runs on a single platform. These are not three separate risks. They are one compounding exposure — and most programs account for them in three separate places with no connection between them.
Where does cyber risk become credit risk? A ransomware event is not just a cybersecurity incident. It is an operational disruption with revenue implications, a vendor risk event if third-party systems are affected, a business continuity trigger, and — if it results in customer loss or litigation — a credit and financial risk as well. The question is not which team owns it. The question is whether anyone in the institution has a single, consolidated view of what it means.
What does our vendor concentration actually look like across all domains? Most vendor risk programs track vendor performance and contract terms. Very few track the aggregate dependency across credit exposure, operational reliance, cyber access, and business continuity assumptions simultaneously — for the same vendor. That aggregate dependency is the actual risk. The individual tracking is just administration.
Are our risk ratings consistent or are they department-specific? When operational risk rates a process as "high" and credit risk rates the same process as "medium" because the taxonomies are different, the institution does not have a risk rating — it has two opinions. Examiners are increasingly asking which one is right. The correct answer is neither, because they are not measuring the same thing.
The Three Structural Shifts That Break the Silo
Integrating risk management is not primarily a technology problem. Technology is the enabler. The harder work is organizational and architectural.
First: Unified taxonomy before unified data. Before any institution can see its risk picture whole, it has to agree on what words mean. What is a "critical" vendor? What constitutes a "high" operational risk? What is the threshold for escalation across domains? Taxonomy inconsistency is the reason risk data cannot be aggregated — not the platform.
Second: Risk relationships, not just risk records. A connected risk program does not just store risks. It maps the relationships between them. The credit exposure is tied to a vendor. The operational dependency embedded in a business continuity assumption. The cyber access that sits inside a vendor contract. These relationships are where aggregate exposure actually lives — and they are invisible in any system that treats each domain as a separate record-keeping function.
Third: Reporting that crosses committee lines. As long as credit risk reports to the credit committee, operational risk reports to the operational risk committee, and cyber reports to the IT steering committee — with no synthesis above all three — the institution's leadership will never have an enterprise risk view. They will have three functional views. The board deserves better. Examiners expect better.
The Honest Assessment
If your institution cannot answer the question — what is our aggregate exposure to our top five vendors across credit, operational, cyber, and continuity dimensions simultaneously — in under 30 minutes, you do not have an integrated risk program.
You have a collection of risk programs.
That distinction did not matter much when examiners were checking boxes. It matters enormously now that they are asking questions.
The institutions that will define best practice in the next examination cycle are not the ones with the most sophisticated individual risk functions. They are the ones that figured out how to make those functions speak to each other — and built a governance structure that acts on what the conversation reveals.
The silo is not a legacy problem to be patient with.
It is the risk.
This is the third article in an ongoing series on the evolving state of enterprise risk management at financial institutions. Previous pieces examined AI governance and defensibility and data integrity as a core risk function.