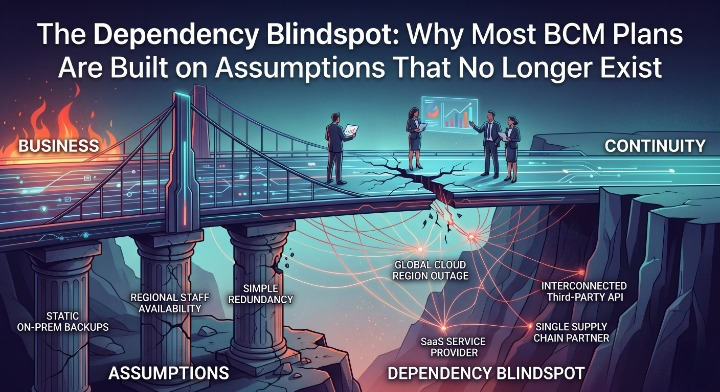
The Dependency Blindspot: Why Most BCM Plans Are Built on Assumptions That No Longer Exist

The Dependency Blindspot: Why Most BCM Plans Are Built on Assumptions That No Longer Exist
Business Continuity Management | William C. Hord
Your business continuity plan is probably well-written.
It likely reflects genuine thought about scenarios, recovery priorities, and response steps. It has been reviewed, approved, and tested. It satisfies examination requirements. The documentation is solid.
And it is probably built on a picture of your operational environment that no longer accurately exists.
Not because your team was careless. Because the environment changed faster than the plan did.
The systems your institution depends on today are not the systems your BCM framework was designed around. The dependencies are deeper, less visible, and far more interconnected than most business continuity programs have formally mapped. And when something fails — when a cloud platform goes down, a third-party integration breaks, or a vendor's infrastructure becomes unavailable — the gap between what the plan assumes and what actually happens becomes impossible to ignore.
That gap is the real BCM problem of 2026.
What the Previous Two Articles Established
In the first article in this series, we examined why BCM execution — not documentation — is where institutions now fail examinations. Plans exist. The ability to operate under stress, adapt in real time, and prove resilience across interconnected systems is what breaks down.
In the second article, we examined why cyber risk can no longer be managed as an IT problem. A ransomware event is not a data loss incident. It is an operational shutdown — and it propagates through exactly the kind of interconnected dependency chains that most BCM programs have never fully mapped.
Both articles pointed at the same underlying issue without naming it directly.
Organizations don't understand their own dependency chains well enough to plan around them, respond through them, or defend them to examiners.
That is the subject of this article.
The Architecture of Modern Operational Failure
A generation ago, operational failures at financial institutions were largely local. A server went down. A branch flooded. A system outage affected a single application. The failure was bounded by the physical and logical limits of what broke.
That is not how failures propagate today.
Modern financial institution operations are built on layered dependencies — cloud platforms running core applications, SaaS providers handling critical workflows, third-party integrations connecting payment systems, identity providers governing access to nearly everything, and API connections threading through functions that were previously independent.
When any one of those layers fails, the impact does not stay contained to that layer. It cascades.
A cloud provider outage takes down not one system but every system hosted on that infrastructure — including systems your BCM plan categorizes as separate, independent recovery priorities. A compromised identity provider does not affect one application. It potentially locks your team out of the recovery environment itself. A vendor integration failure does not interrupt one business process. It interrupts every business process that depends on data flowing through that integration.
The failure is no longer bound. It is networked.
And most BCM programs were designed for bounded failures.
The Dependency Chain Problem
Here is the core issue stated plainly.
Most institutions know what systems they operate. Very few institutions know the full dependency chain beneath each of those systems — what those systems depend on, what depends on them, and what the second and third-order impacts are when any node in that chain becomes unavailable.
This is not a criticism. It is an architectural reality that most BCM frameworks have not kept pace with.
Consider what a single "critical system" actually rests on today.
Your core banking platform depends on a cloud hosting provider. That cloud provider depends on a physical data center in a specific geography. Your core banking platform connects to a payment processing integration managed by a third-party vendor. That vendor's platform also connects to your fraud detection system, your compliance monitoring tools, and your customer-facing digital banking interface. Your recovery strategy assumes your team can access the core banking environment using administrative credentials — credentials managed by an identity provider that is itself a SaaS platform hosted in the cloud.
If the cloud provider has an outage, you have lost not just core banking but every system in that dependency chain simultaneously. Your recovery plan, which was built to restore core banking as a priority, cannot execute because the identity environment needed to authorize recovery access is also unavailable.
This is not a theoretical scenario. Variations of it have caused real operational failures at real institutions. The dependency chain was never mapped. The BCM plan was built on the assumption that systems could be recovered independently. And when the outage came, the assumption collapsed.
What Examiners Are Now Testing
The examination posture around business continuity has shifted significantly and continues to shift.
The Federal Reserve, OCC, and FDIC have aligned around an operational resilience framework that explicitly evaluates whether institutions can identify and manage dependencies supporting critical business services — not just whether they have documented recovery procedures for those services.
The FFIEC's updated guidance on business continuity and resilience requires institutions to map dependencies at the service level — including technology, vendors, staff, facilities, and data — and to demonstrate that recovery strategies account for the failure of those dependencies, not just the failure of the primary system.
What examiners are probing now is not the plan. It is the map.
- What are your critical business services?
- What dependencies — systems, vendors, cloud platforms, integrations — support each service?
- What happens to each service when any one of those dependencies fails?
- Have you tested recovery scenarios that include dependency failures, not just primary system failures?
- Can you demonstrate that your RTOs are achievable given how your dependencies are actually structured?
The institutions that answer these questions confidently are the ones that have mapped their dependency chains with genuine rigor. The institutions that struggle are the ones whose BCM documentation describes systems — but not the interconnected architecture those systems actually run on.
The Three Dependency Failures That Appear Most Frequently
Across BCM programs at financial institutions, three categories of dependency failure appear most consistently — and most consequentially.
Cloud platform concentration without recovery alternatives. Institutions have migrated significant portions of their technology infrastructure to cloud platforms, often without formally assessing what that concentration means for their BCM assumptions. When a cloud provider experiences a regional outage, recovery strategies that assume independent system restoration become un-executable. The systems aren't down individually. They're down collectively because they share the same infrastructure layer.
Third-party integration failures that cascade across functions. Financial institutions rely on third-party integrations for an expanding range of critical functions — payments, compliance monitoring, fraud detection, digital banking, identity management. These integrations are often treated as vendor relationships in the vendor risk program and as system inputs in the BCM program, but rarely as dependency chains that connect multiple critical services. When an integration fails, the impact crosses every function that depends on it — and BCM plans that were written at the function level may not recognize the scope of what is actually affected.
Identity and access dependencies in recovery environments. This is the dependency that appears most often as a critical gap in examinations and after-action reviews. Recovery strategies assume that the team can access systems and execute restoration procedures. Those assumptions rest entirely on identity and access management infrastructure functioning correctly. When that infrastructure is compromised — as it is in nearly every significant ransomware event — the recovery plan's first step becomes inaccessible. The institution cannot authenticate. It cannot be authorized. The plan exists. It cannot be executed.
What a Dependency-Aware BCM Program Actually Requires
Moving from a documentation-based BCM program to a dependency-aware one requires changes that go beyond updating the plan document.
Map at the service level, not the system level. The starting point is identifying critical business services — not critical systems. A critical business service is the end-to-end capability the institution provides: member account access, payment processing, lending origination, compliance reporting. Once the service is defined, the full dependency stack beneath it can be mapped — every system, vendor, integration, cloud platform, and human capability required to deliver it. This mapping will reveal dependencies that system-level inventories never surface.
Treat third-party integrations as first-party dependencies. Vendor risk programs track third-party performance and contract terms. BCM programs need to treat critical third-party integrations as core infrastructure — with the same dependency mapping, recovery assumptions, and testing requirements applied to owned systems. The distinction between "our systems" and "vendor systems" is not meaningful when the vendor's system is inside your critical service delivery chain.
Test the dependency chain, not just the primary system. BCM testing that validates whether a primary system can be restored is necessary but no longer sufficient. Testing that matters is testing that introduces dependency failures — cloud platform unavailability, integration outages, identity provider compromise — and evaluates whether recovery strategies remain executable when the supporting infrastructure is also affected. If the test only works when dependencies are functioning normally, it is not testing the scenarios that actually fail.
Document recovery assumptions explicitly. Every recovery strategy rests on assumptions — about what will be available, what can be accessed, what will function correctly during a disruption. Those assumptions need to be documented explicitly and reviewed regularly. When an assumption no longer holds — because a vendor changed their architecture, a cloud provider updated their service model, or an integration was modified — the recovery strategy built on that assumption needs to be updated. Silent assumption drift is how plans become unreliable without anyone realizing it.
The Honest Assessment
The question to ask of your BCM program is not whether the plans are complete.
The question is whether the plans reflect how your institution actually operates today.
- Do your recovery strategies account for cloud platform concentration risk?
- Are your critical third-party integrations mapped as dependencies within your critical service chains?
- Does your identity and access recovery strategy address scenarios where the identity environment itself is compromised?
- Have you tested recovery under conditions where multiple dependencies fail simultaneously — not just the primary system?
If the answer to any of those questions is uncertain, the plan may be thorough and the dependency chain may still be invisible.
That invisibility is not a documentation problem. It is a resilience problem. And it is exactly where examination scrutiny is now focused.
The institutions that close this gap will do so not by writing better plans but by building a more accurate picture of the operational environment those plans are supposed to protect.
The plan is only as good as the map it is drawn from.
This is the third article in an ongoing series on the evolving state of business continuity management at financial institutions. Previous pieces examined BCM execution under stress and cyber risk as a continuity crisis.